- Topic1/3
32k Popularity
10k Popularity
16k Popularity
7k Popularity
16k Popularity
- Pin
- 🎉 Gate Square Growth Points Summer Lucky Draw Round 1️⃣ 2️⃣ Is Live!
🎁 Prize pool over $10,000! Win Huawei Mate Tri-fold Phone, F1 Red Bull Racing Car Model, exclusive Gate merch, popular tokens & more!
Try your luck now 👉 https://www.gate.com/activities/pointprize?now_period=12
How to earn Growth Points fast?
1️⃣ Go to [Square], tap the icon next to your avatar to enter [Community Center]
2️⃣ Complete daily tasks like posting, commenting, liking, and chatting to earn points
100% chance to win — prizes guaranteed! Come and draw now!
Event ends: August 9, 16:00 UTC
More details: https://www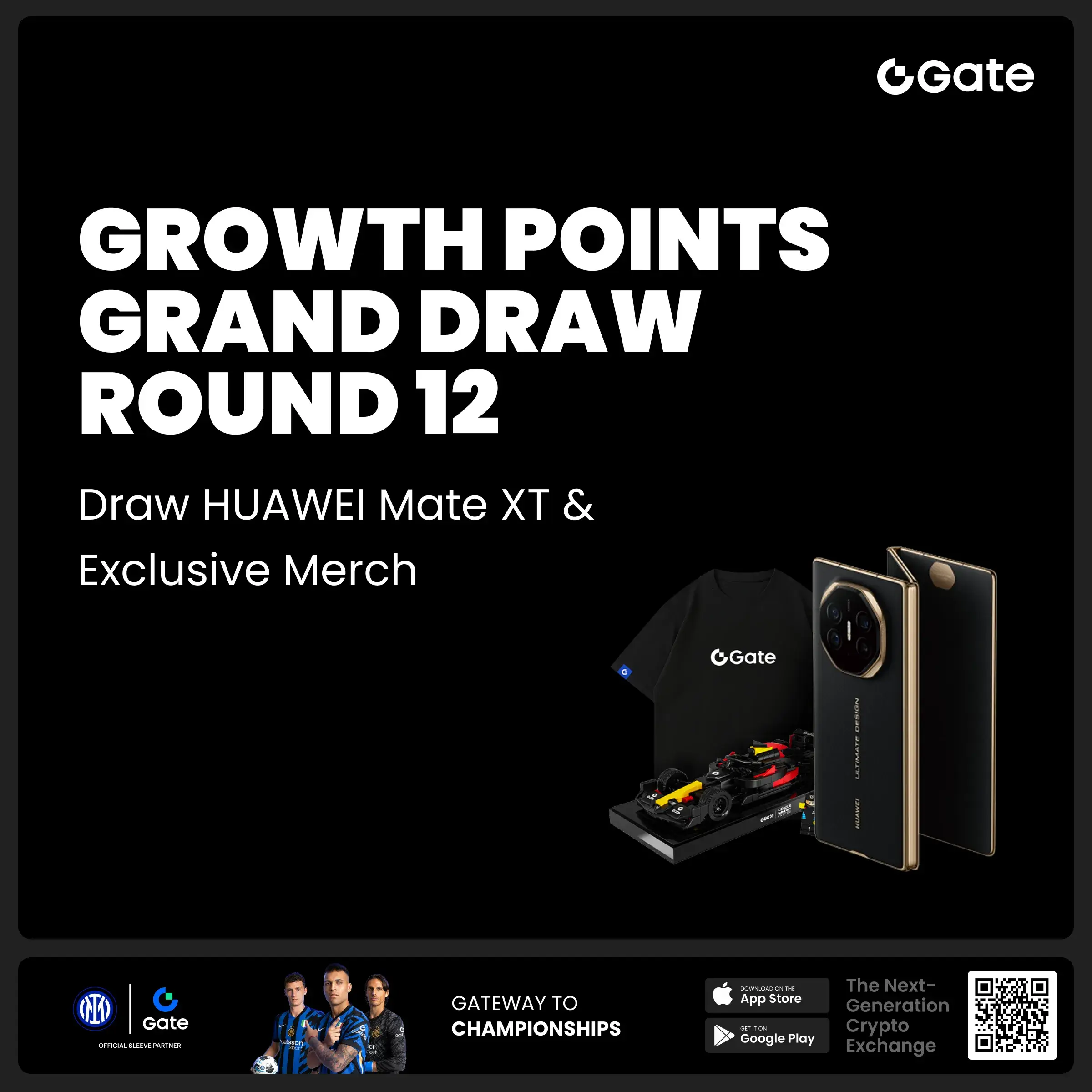
- #Gate 2025 Semi-Year Community Gala# voting is in progress! 🔥
Gate Square TOP 40 Creator Leaderboard is out
🙌 Vote to support your favorite creators: www.gate.com/activities/community-vote
Earn Votes by completing daily [Square] tasks. 30 delivered Votes = 1 lucky draw chance!
🎁 Win prizes like iPhone 16 Pro Max, Golden Bull Sculpture, Futures Voucher, and hot tokens.
The more you support, the higher your chances!
Vote to support creators now and win big!
https://www.gate.com/announcements/article/45974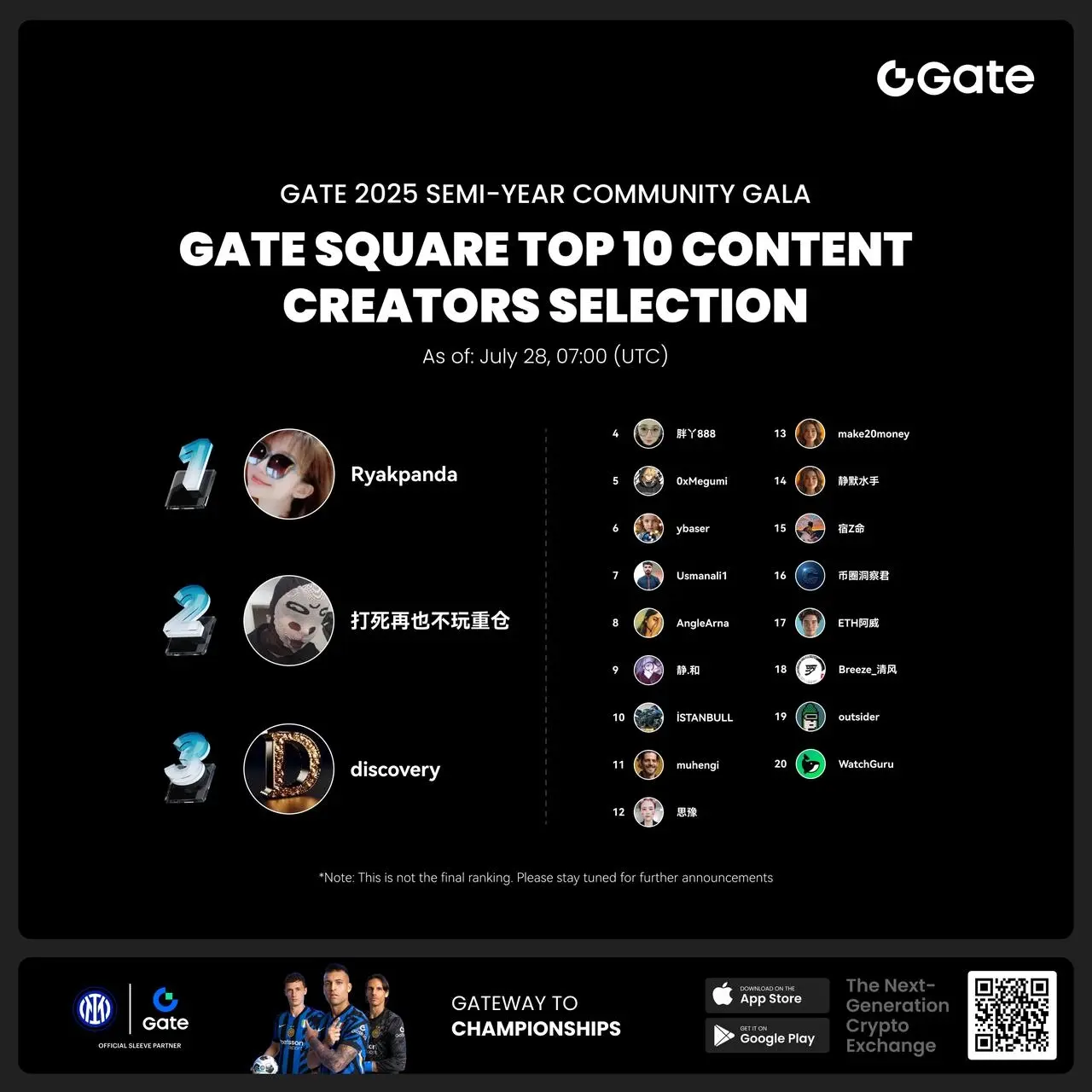
GMX Exploiter Return $40M Days After Hack, Token Zooms Higher
The attacker who drained over $40 million from GMX’s V1 contracts earlier this week has started returning funds, suggesting they’ve accepted the project’s $5 million white-hat bounty.
The first signs came Friday via an on-chain message: “ok, funds will be returned later.”
Hours later, over $10.5 million in FRAX was sent back to GMX’s deployer wallet. Security firm PeckShield flagged the returns, which appear to be just the start, with more funds expected to follow.
GMX is now trading at $13.15 having risen by 13% over the past 24 hours.
Later on, over $40 million in various tokens were returned to the GMX Security Committee MultiSig address, Lookonchain noted.
The breach, one of the largest DeFi exploits of the year, targeted GMX’s GLP pool on Arbitrum. It exploited a re-entrancy flaw in the OrderBook contract, allowing the attacker to manipulate short positions on BTC, inflate GLP’s valuation, and redeem it for outsized profits across USDC, WBTC, WETH, and FRAX.
Reentrancy is a common bug that allows exploiters to trick a smart contract by repeatedly calling a protocol to steal assets. A call authorizes the smart contract address to interact with a user’s wallet address.
GMX responded by halting V1 trading and minting across both Arbitrum and Avalanche. A bug bounty worth more than 10% of the stolen funds was offered, with a promise of no legal pursuit if the full amount was returned within 48 hours (which the hacker seems to have adhered to as of European morning hours Friday).
View Comments