- Topic1/3
793 Popularity
5k Popularity
9k Popularity
4k Popularity
17k Popularity
- Pin
- #Gate 2025 Semi-Year Community Gala# voting is in progress! 🔥
Gate Square TOP 40 Creator Leaderboard is out
🙌 Vote to support your favorite creators: www.gate.com/activities/community-vote
Earn Votes by completing daily [Square] tasks. 30 delivered Votes = 1 lucky draw chance!
🎁 Win prizes like iPhone 16 Pro Max, Golden Bull Sculpture, Futures Voucher, and hot tokens.
The more you support, the higher your chances!
Vote to support creators now and win big!
https://www.gate.com/announcements/article/45974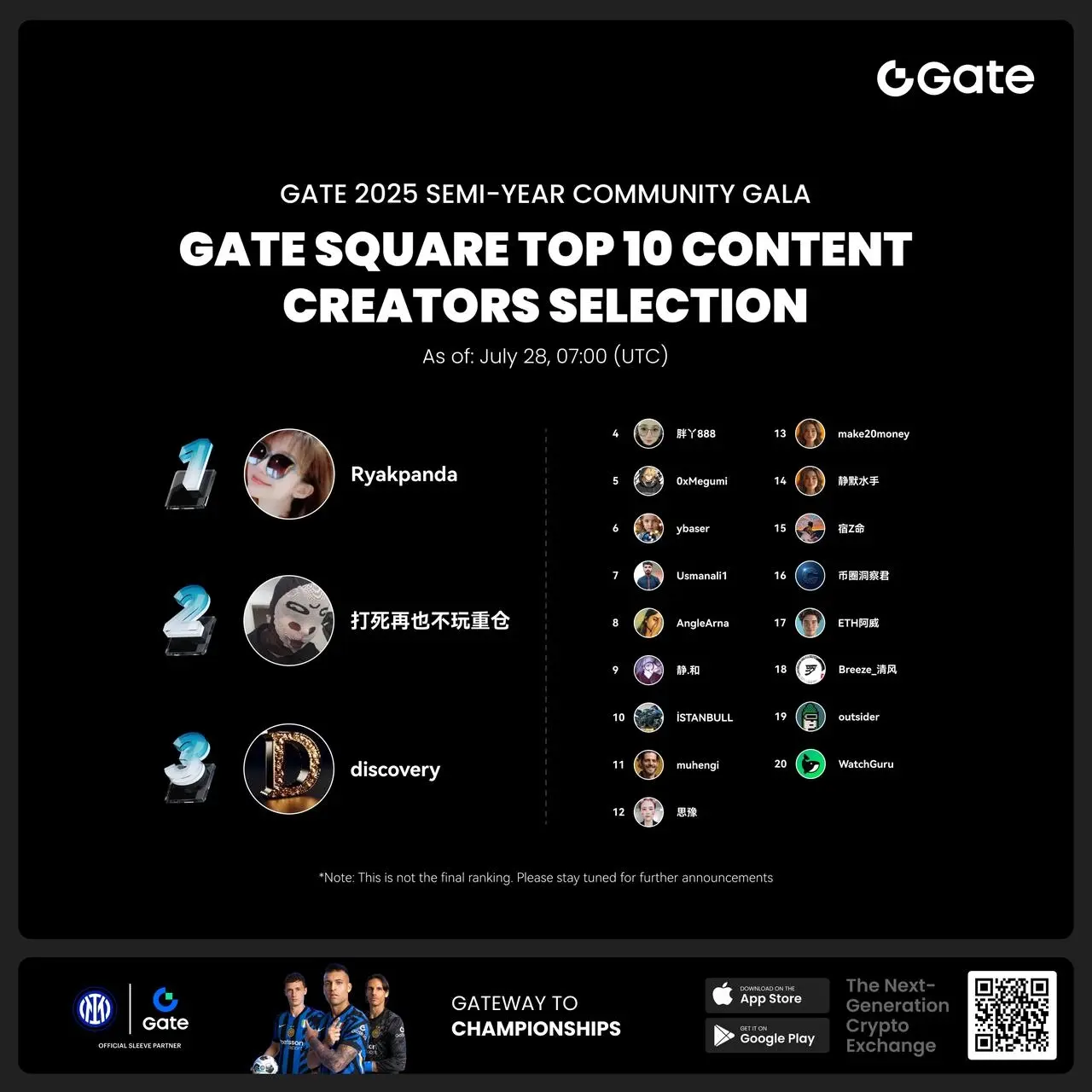
- 🎉 Hey Gate Square friends! Non-stop perks and endless excitement—our hottest posting reward events are ongoing now! The more you post, the more you win. Don’t miss your exclusive goodies! 🚀
1️⃣ #ETH Hits 4800# | Market Analysis & Prediction: Boldly share your ETH predictions to showcase your insights! 10 lucky users will split a 0.1 ETH prize!
Details 👉 https://www.gate.com/post/status/12322612
2️⃣ #Creator Campaign Phase 2# |ZKWASM Topic: Share original content about ZKWASM or its trading activity on X or Gate Square to win a share of 4,000 ZKWASM!
Details 👉 https://www.gate.com/post/st
United Nations reveals: Hacker gang laundered $147.5 million involved in 97 cases of Crypto Assets attacks.
A confidential report from the United Nations indicates that a notorious Hacker gang stole funds from a certain Crypto Assets exchange last year and laundered $147.5 million through a certain Virtual Money platform in March of this year.
The inspectors reported to the UN Security Council Sanctions Committee that they are investigating 97 cyber attacks against encryption companies that occurred between 2017 and 2024, involving approximately $3.6 billion. This includes a $147.5 million theft from a certain Crypto Assets exchange at the end of last year, which was laundered in March of this year.
The U.S. government imposed sanctions on the virtual money platform in 2022. In 2023, two co-founders of the platform were accused of assisting in money laundering over $1 billion, involving a cybercrime organization related to a certain country.
According to a study by a Crypto Assets investigation expert, the hacker group laundered $200 million worth of Crypto Assets into fiat currency between August 2020 and October 2023.
In the field of cybersecurity, this hacker group has long been regarded as the mastermind behind large-scale cyberattacks and financial crimes. Their targets span the globe, involving various sectors such as banking systems, crypto assets exchanges, government agencies, and private enterprises. Below, we will analyze several typical cases, revealing how this group implements these astonishing attacks through complex strategies and technical means.
social engineering and phishing attacks
According to European media reports, the hacker group previously targeted military and aerospace companies in Europe and the Middle East. They posted fake job advertisements on social media platforms to lure job seekers into downloading PDF documents containing malicious executable files, thereby implementing phishing attacks.
These types of attacks primarily utilize psychological manipulation techniques to lure victims into lowering their guard and performing dangerous actions such as clicking links or downloading files. Hackers can exploit vulnerabilities in the victim's system through embedded malware to attack and steal sensitive information.
In a six-month operation against a certain Crypto Assets payment provider, hackers employed similar tactics. They sent fake job offers to engineers while launching distributed denial of service attacks and attempted brute-force password cracking, ultimately resulting in the company being robbed of $37 million.
Multiple incidents of attacks on cryptocurrency exchanges
On August 24, 2020, a wallet at a certain Canadian crypto assets exchange was hacked.
On September 11, 2020, a certain blockchain project suffered an unauthorized transfer of $400,000 from multiple wallets controlled by the team due to a private key leak.
On October 6, 2020, another crypto assets exchange had $750,000 worth of encryption assets illegally transferred from its hot wallet due to a security vulnerability.
At the beginning of 2021, the funds from these attack incidents were gathered into the same address. Subsequently, the attacker deposited a large amount of ETH through a certain mixing service and withdrew it in batches over the next few days.
By 2023, after multiple transfers and exchanges, the stolen funds ultimately converged at addresses associated with other security incident fund aggregations. According to fund tracking, the attackers gradually sent the stolen funds to deposit addresses of certain withdrawal platforms.
The founder of a certain mutual insurance platform was attacked by a Hacker.
On December 14, 2020, the personal account of the founder of a mutual insurance platform was hacked, resulting in the theft of 370,000 platform coins, worth approximately 8.3 million dollars.
Stolen funds were transferred between multiple addresses and exchanged for other Crypto Assets. The Hacker performed fund obfuscation, decentralization, and aggregation through these addresses. Some funds were cross-chain to the Bitcoin network, then back to the Ethereum network, after which they were obfuscated through a mixing platform and finally sent to a withdrawal platform.
In the following days, one of the hacker addresses will send over 2500 ETH to a certain mixing service. A few hours later, another related address starts the withdrawal operation.
The hacker transferred part of the funds to the withdrawal address that was involved in the previous incident through a series of transfers and exchanges.
From May to July 2021, the attackers transferred 11 million USDT to the deposit address of a certain exchange.
From February to March 2023, the attacker sent 2.77 million USDT to the deposit address of a certain P2P exchange through an intermediary address.
From April to June 2023, the attacker again sent 8.4 million USDT to the deposit address of another withdrawal platform via the same intermediary address.
Two DeFi project attack incidents
In August 2023, two DeFi projects were attacked one after the other. The first project lost 624 ETH, and the second project lost 900 ETH. The stolen ETH was subsequently transferred to a mixing service.
After depositing ETH into the mixing service, the attacker immediately began to withdraw funds in batches to several different addresses. On October 12, 2023, the funds withdrawn from the mixing service were consolidated into a new address.
In November 2023, this aggregation address began transferring funds, which were ultimately sent to the deposit addresses of two commonly used withdrawal platforms through intermediaries and exchanges.
Summary
By analyzing the activities of this hacker group in recent years, we can summarize their main money laundering methods: after stealing Crypto Assets, they usually perform repeated cross-chain operations and then use mixers for fund obfuscation. After obfuscation, they will withdraw the stolen assets to the target address and send them to a fixed group of addresses for withdrawal operations. The stolen Crypto Assets are mainly deposited into two specific withdrawal platform deposit addresses, and then exchanged for fiat currency through over-the-counter trading services.
This series of large-scale attacks poses a significant challenge to the security of the Web3 industry. Relevant security agencies will continue to monitor the movements of this hacker group and analyze their money laundering techniques in order to assist project parties, regulatory agencies, and law enforcement in combating such crimes and recovering stolen assets.